Background
One of the largest blockchain and digital asset derivatives companies in the world. Their businesses include trading and finance, education, data and research, social charity, investment and incubation, decentralization and infrastructure solution.
Challenge
Due to the fact that the majority of employees work remotely, the company must both ensure the data security of remote office computers through compliance settings, remote locking, remote wiping etc., while also making corporate resources like software and VPN configurations as convenient and accessible as possible for their employees. To ensure that workers can use the new computers right out of the box when they receive them, IT must configure devices for new hires in a zero-touch manner.
The customer was using a UEM (Workspace One) software to manage all the Mac and iPhone devices in the enterprise, but since UEM is a multi-platform unified endpoint management software, its drawbacks were obvious:
- Each platform’s management capabilities had been compromised, making it impossible to update to the most recent versions of macOS and iOS. This is unacceptable for the blockchain industry, as it means that user devices will be out of the security control of the enterprise, which may cause irreparable damage.
- Secondly, UEM is gradually failing to meet the demand in terms of the depth of Apple device management, such as device details, logs and granularity, APIs, etc.
Story
The way people work has been irrevocably altered by mobile technology. Mobile devices enable employees to work almost anywhere, at any time, and provide them with simple access to company and customer data. This labor flexibility can come at a cost. As the number of mobile devices deployed increases, so do the security risks. Security threats grow as more mobile devices are used, and vice versa.
Businesses that invest in smartphones, tablets, and other mobile devices for use by their staff have security concerns and want to make sure their data is being used responsibly.
Sensitive corporate information might not be fully shielded from a compromised device by authentication only. Administrators must also make sure that end users are using reliable devices to access business apps and services. This calls for ongoing security and access policy development while preserving the privacy and productivity of end users.
Another crucial factor in choosing an MDM solution is the integration of current Okta authentication services and device trust. Only trusted devices can access your Okta-managed applications, which means that only compliant devices can access enterprise resources, ensuring access security. By eliminating threats at the source, Okta Device Trust integration ensures that only known and secure devices can access your Okta-managed applications.
Results
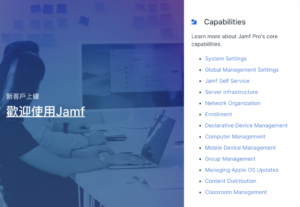
The use of Jamf Pro device management software and full Okta feature integration reduces enterprise information security risks to a minimum by achieving unified authentication and strengthening end-device and data security:
- Use Jamf Pro to manage Apple devices to get the latest version of macOS and iOS and support Apple chips at the first time, without worrying about unknown risks caused by users upgrading their systems.
- Okta device trust prevents potential security risks.
- More detailed device asset information gives managers a clear picture of device status.
- Jamf Pro API integration with Splunk and centralized visualization of log reports.
- Convenient software design patch management.
- More effective technical support guarantee.
The customer was well-versed in MDM and aware of its requirements: it needed to select the appropriate UEM replacement and collaborate with a partner with considerable knowledge. Together, we could resolve the technical issues that arise throughout the equipment management process in an efficient manner. The customer basically opted to choose Jamf Pro
as the ultimate Apple device management solution after studying the Jamf product and receiving a number of technical communications, and they selected SolutionKeys to handle their procurement, implementation, training, and other needs. In order to express our gratitude to the client for their confidence and appreciation, we actively collaborated with them in the ensuing relationship and assisted them in finding solutions that were centered on their needs, which significantly enhanced their IT operations.
Industry
Blockchain、Internet
Feature
Security:
- Restrictions
- Lock, wipe and restart
- Software upgrades
- Patch management
Configuration Management:
- Configuration profiles
- Policies
- Scripts